Java - Command Injection 4 (CMD-4)
Running the app on Docker
$ sudo docker pull blabla1337/owasp-skf-lab:java-cmd4$ sudo docker run -ti -p 127.0.0.1:5000:5000 blabla1337/owasp-skf-lab:java-cmd4Reconnaissance
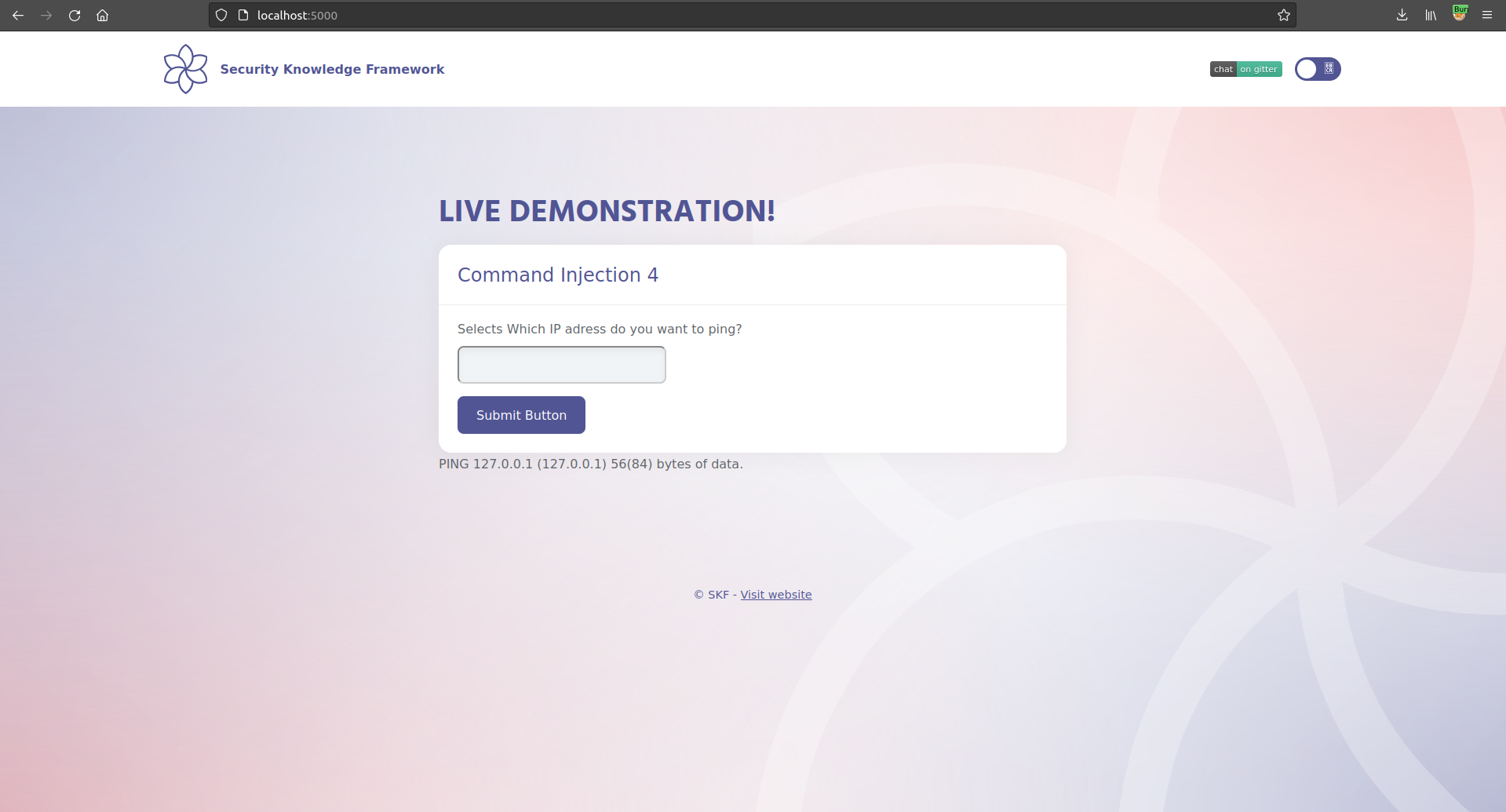
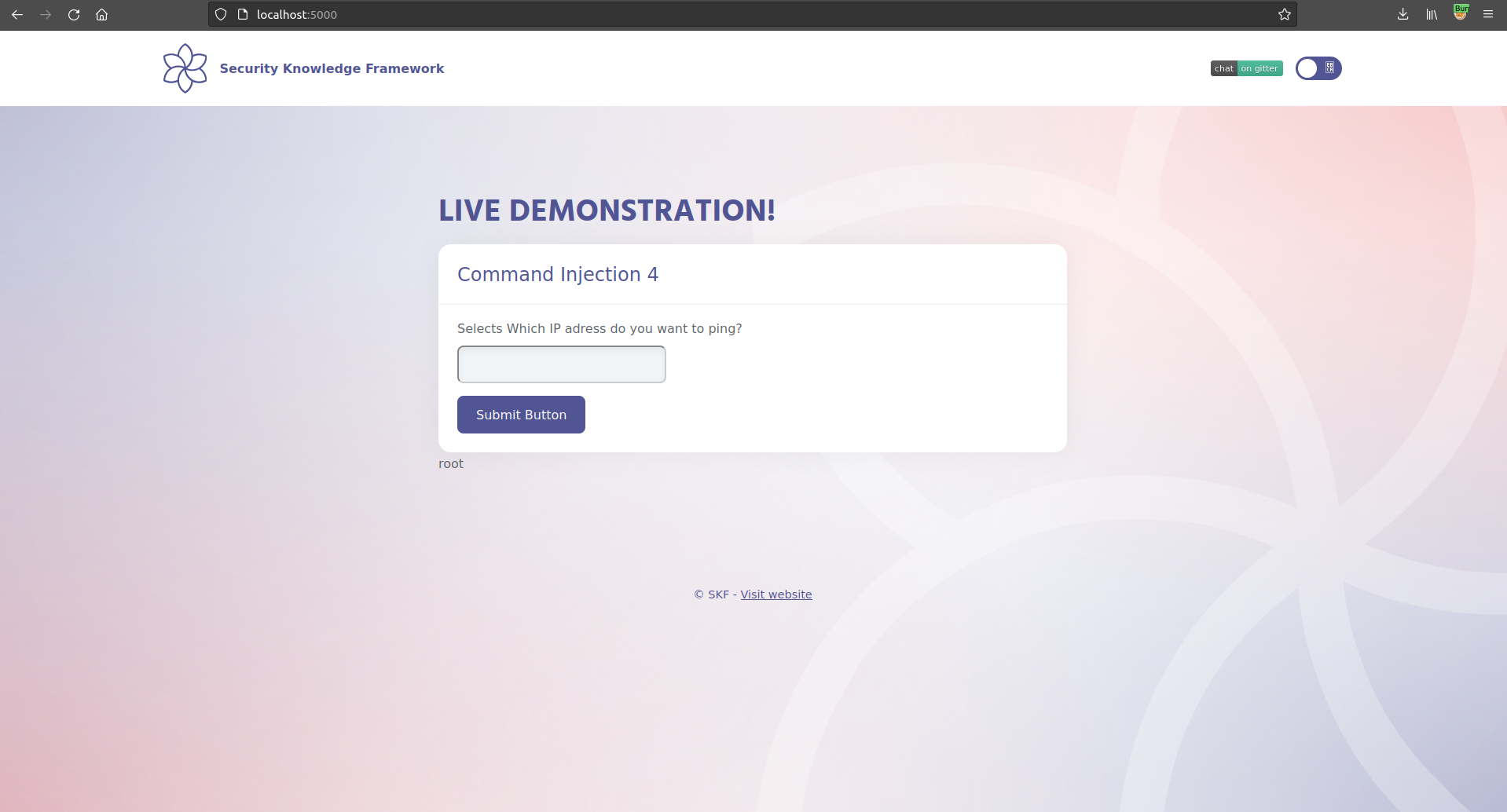
Exploitation
Additional sources
Last updated
Was this helpful?