# Python - XSS-href
## Running the app on Docker
```
$ sudo docker pull blabla1337/owasp-skf-lab:xss-url
```
```
$ sudo docker run -ti -p 127.0.0.1:5000:5000 blabla1337/owasp-skf-lab:xss-url
```
{% hint style="success" %}
Now that the app is running let's go hacking!
{% endhint %}
## Reconnaissance
### Step 1
The application invites you to fill a website in the input box, that will be used from the "visit my website!" link to redirect to it.
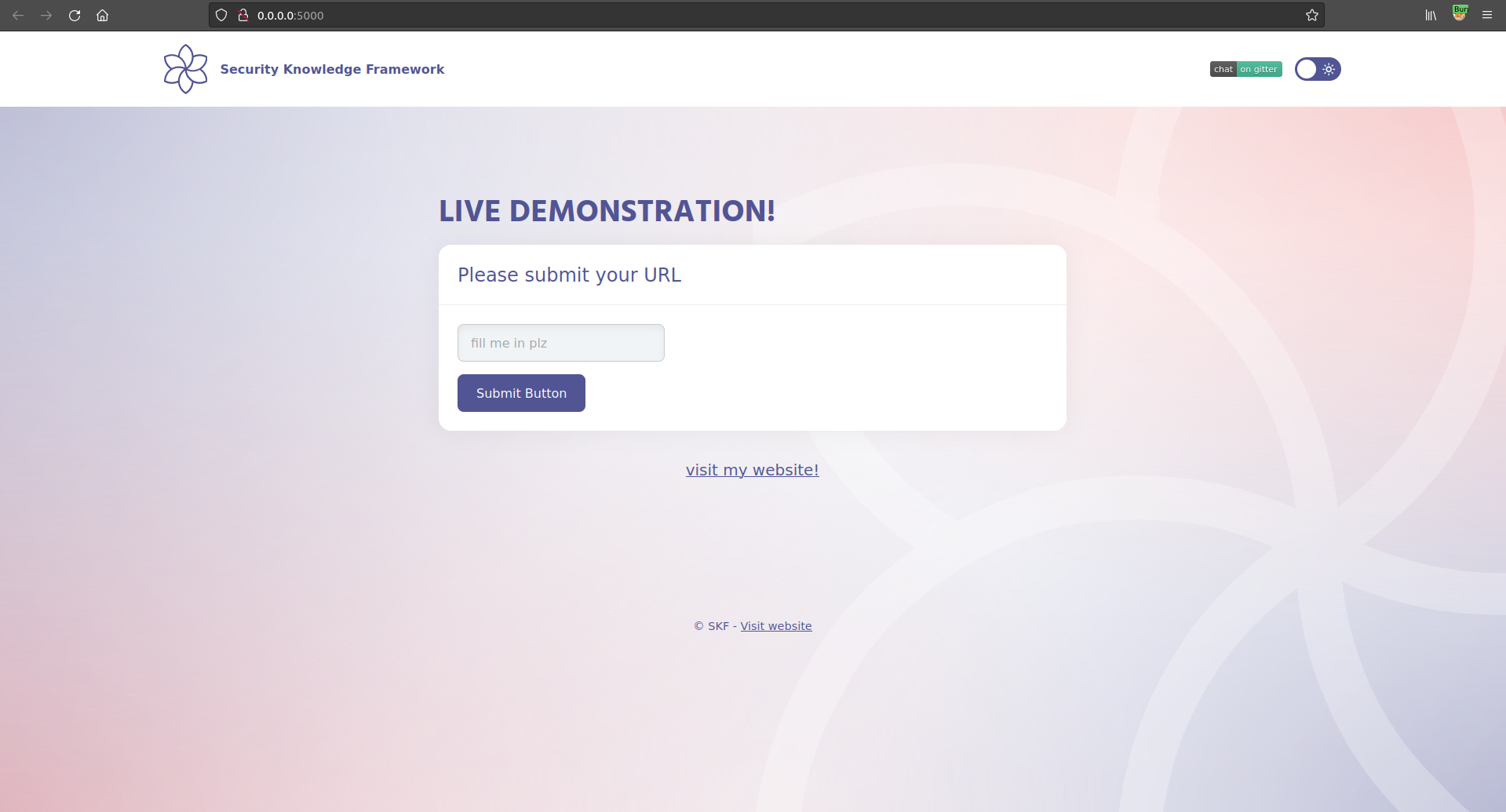
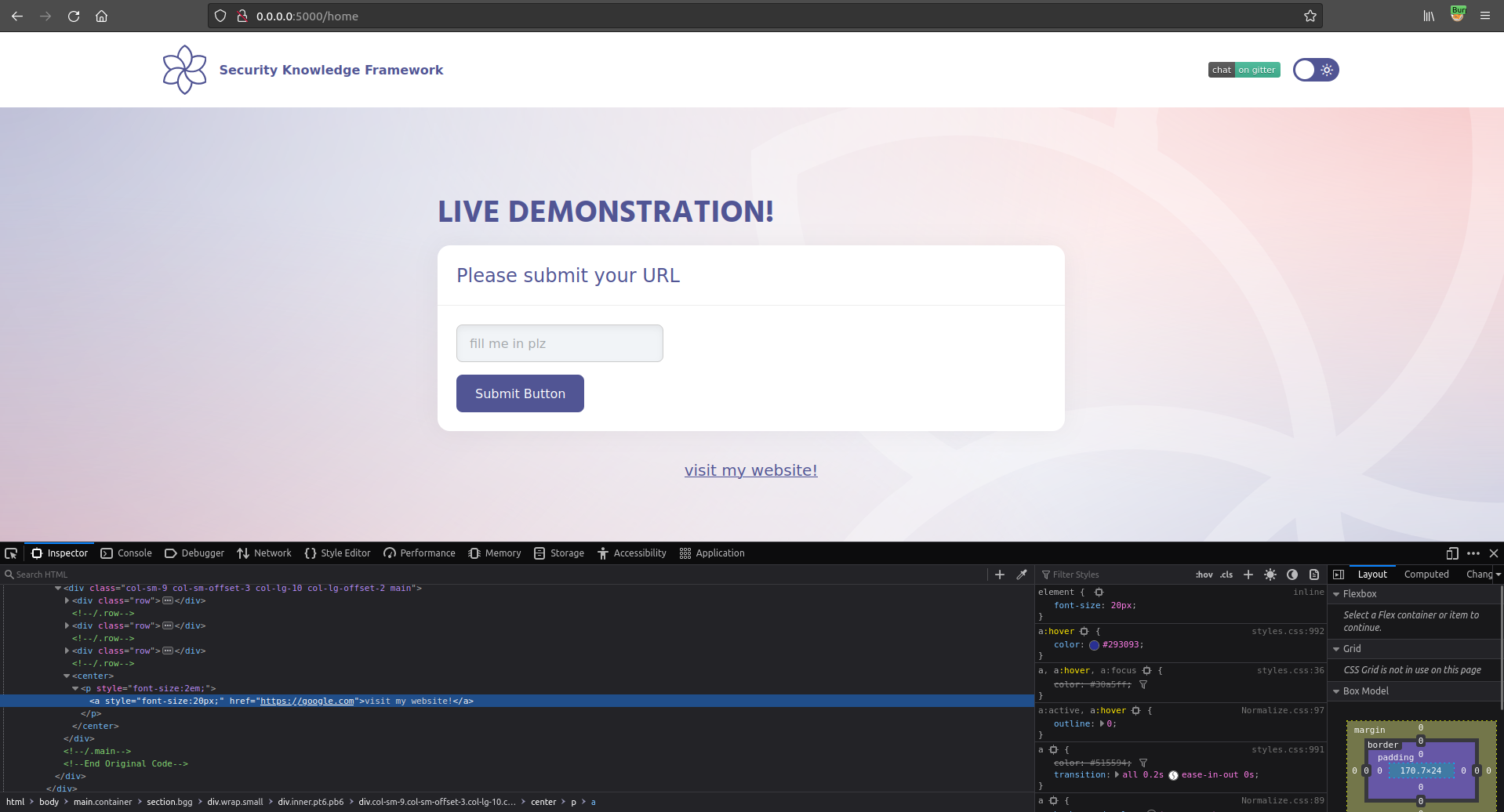
If we insert `https://google.com`, and click on "visit my website!" we will be redirected to the Google website. As we can see in the screenshot below our input is reflected in the page inside an `href` attribute.
#### Step 2
The next step is to see if we could include JavaScript that can be executed in the `href` attribute.
{% hint style="success" %}
href="javascript:JS PAYLOAD"
{% endhint %}
Autoescape is disabled by default so every characters will be reflected in the following snippet in the template.
```markup
```
## Exploitation
#### Step 1
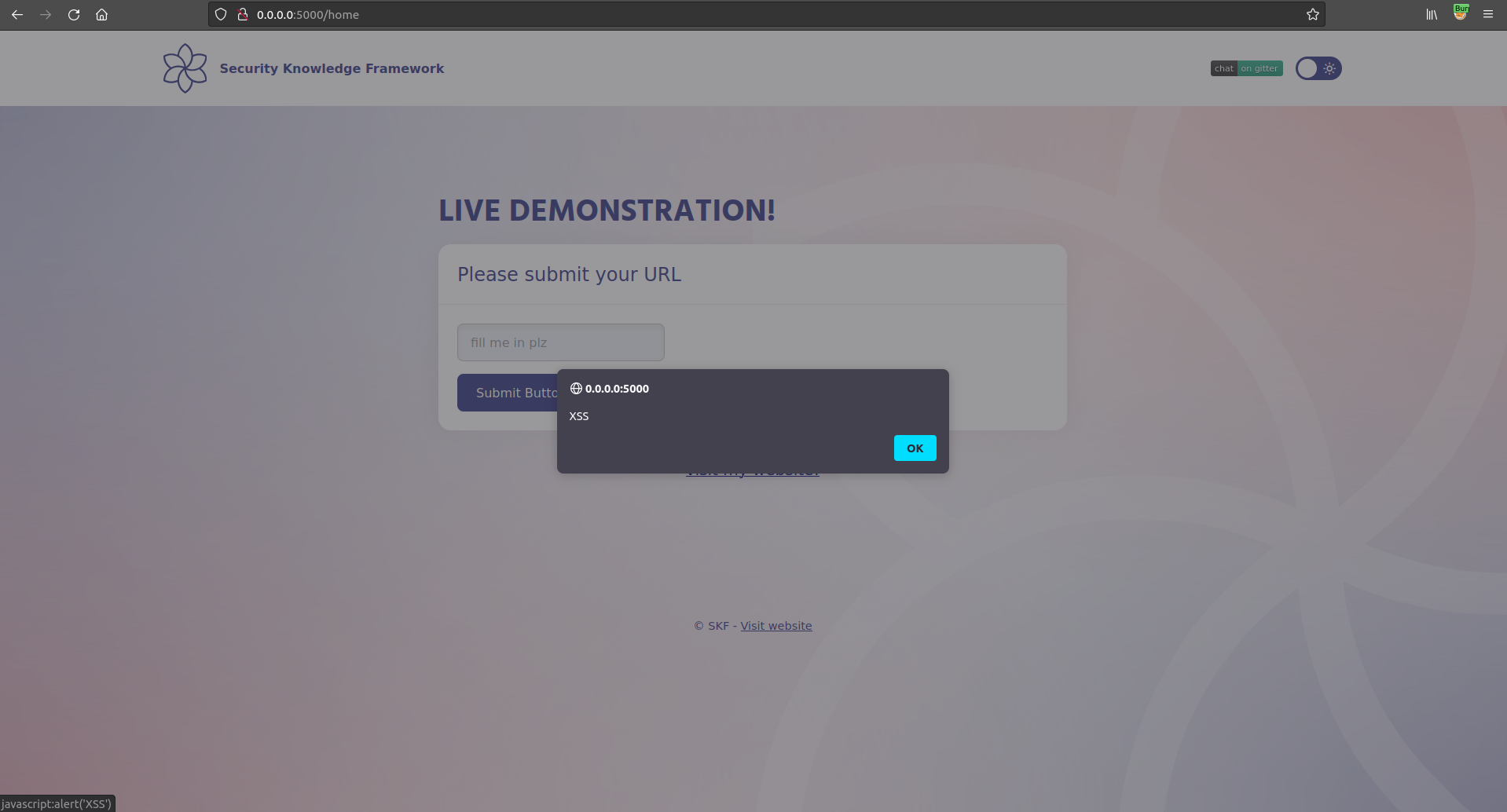
Now we have seen where the user input is being reflected in the href, we can craft the payload to trigger an alert box and exploit our XSS.
```markup
javascript:alert('XSS')
```
and clicking the button, we achieve what we were looking for.
## Additional sources
Please refer to the OWASP testing guide for a full complete description about path traversal with all the edge cases over different platforms!
{% embed url="" %}
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://skf.gitbook.io/asvs-write-ups/cross-site-scripting-href-xss-href/cross-site-scripting-href.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.